
I’ve just gotten to a Starbucks and connected to the wifi. I figured, shoot, why not set up my own VPN on a Digital Ocean droplet that I can use when I’m out and about like this?
Choices, choices… initial research led me to decide between OpenVPN or Wireguard as a VPN option. From what I gathered, here’s a nice pros/cons for each, for my use case.
Use case: One to 2 connected devices; used for passthrough traffic when connected to public networks
| Feature | WireGuard | OpenVPN |
| Speed | Much faster | Slightly Slower |
| Security | Uses modern encryption procotols | Highly configurable; can support order encryption protocols |
| Ease | Setup straightforward | More complex, but with much more configuration/customization |
| Battery Use | Low | Higher than Wireguard |
There are a ton of other features for both applications, but I wanted a set it and forget it setup.
There are plenty of resources for a no-hassle install of Wireguard, so I’ll keep it pretty short. However, I did have a decision to make: server-side install vs. Docker.
Since this is my personal site, I’ll give my definition of Docker/containerization:
Now let’s get to installing!
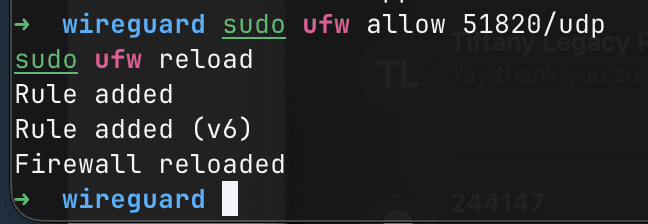
We have one last step before we start our docker contained, and that is to enable our firewall rules. I am using ufw on my system. Run the following and ensure ports match your docker-compose config:
sudo ufw allow 51820/udp
sudo ufw reload
We’ll simply start the container! Ensure you are in the correct directory, and run docker compose up -d
Since this is my first time running this command, Docker will pull all of the required files and start the container (assuming it’s configured correctly 🤞)
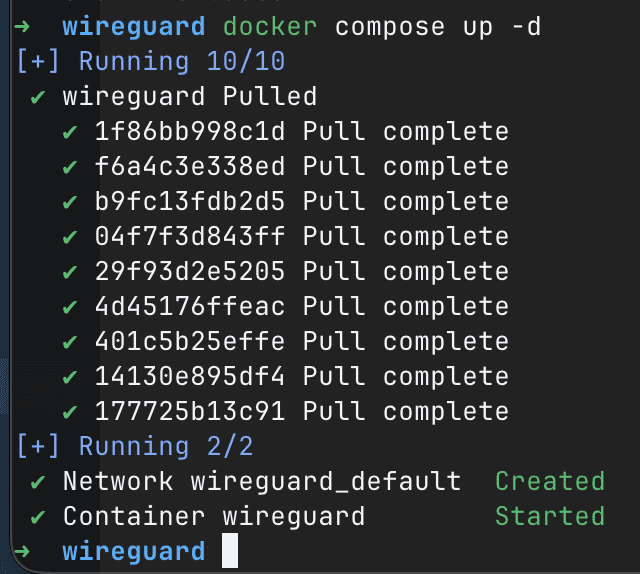
At this point, Wireguard should be up and running! Next step is to get it up and running on your device.
Note: our docker-compose file specified 5 peers, meaning that we basically enabled access for 5 different devices. It is recommended to use a different configuration per-device to ensure that packets are routed to the correct device. If I share a configuration between my laptop and my phone, both devices will receive the same IP on the server and packets may get lost or served incorrectly.
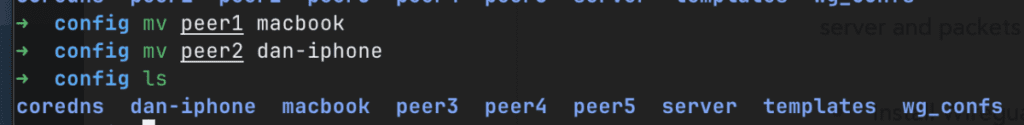
Pull your config files from your server. I’m actually going to rename my peer folders so that I remember which is which in the future:
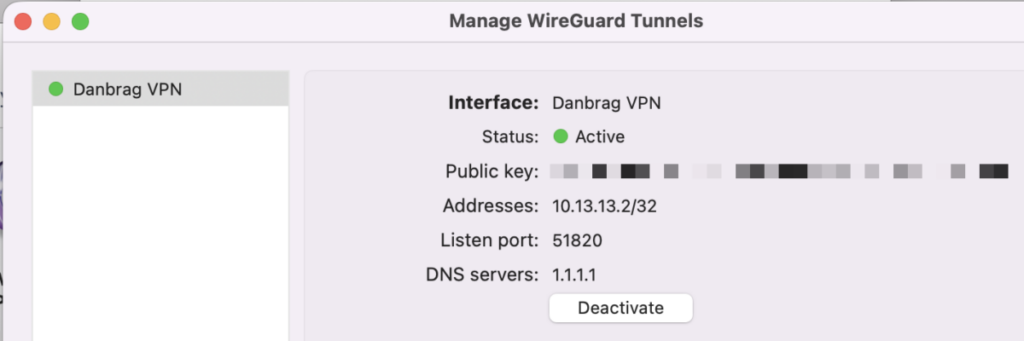
Each folder contains a config file. Use cat to get the contents and copy it into a configuration file to share, or create a new empty configuration on the Wireguard UI (Mac):
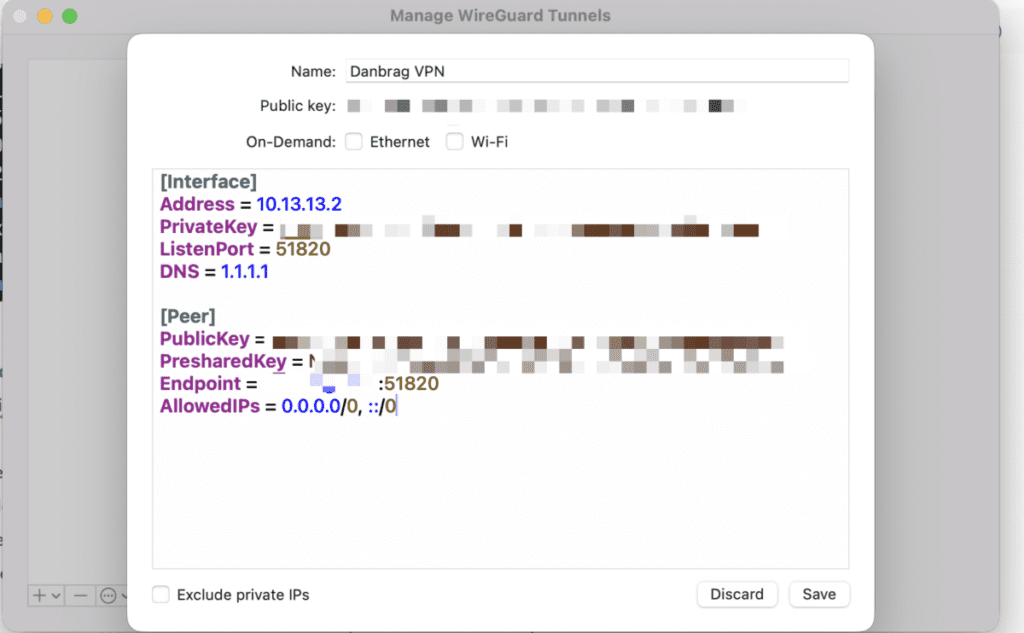
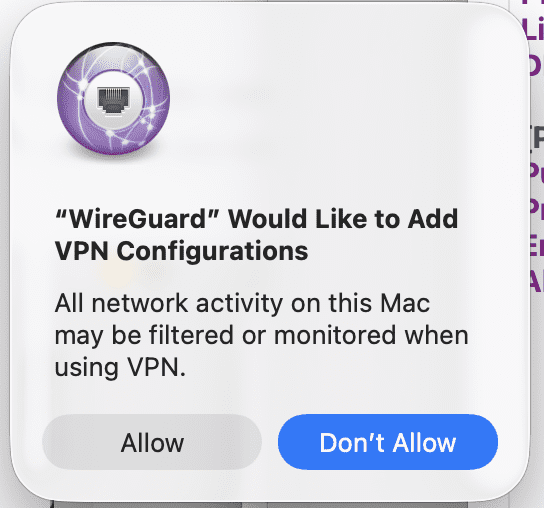
Once you click save, you’ll have to allow Wireguard to add VPN Configurations:
The final step is to click ‘activate’ and let it connect!
For my Phone, I have two options: copy configuration into a file and send it to my phone, or generate a QR code. Luckily for us, Wireguard generates a QR code for us on initialization, saving it as ‘peerX.png’ in the configuration directory.
I downloaded it to my computer quickly via scp and was able to import it by scanning it via the Wireguard app!
scp user@host:/path/to/wireguard/config/dan-iphone/peer2.png ~/Downloads/peer2.png peer2.png
The iPhone app will allow require you to allow Wireguard to add network configurations. One click and one password later, we are up and running!
Let’s ensure our IP now reflects our VPS IP.
The easiest way, and with less ads, is to run curl ifconfig.me. This returns your IP address. Let’s test it out on my laptop. I’ll run that command before, and after enabling:
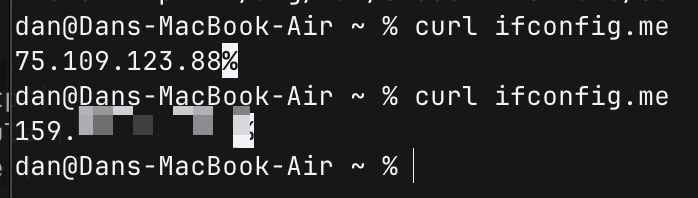
Looks like we’re in business!
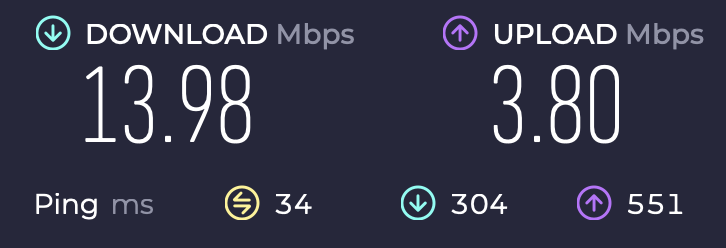
I’m currently using a public Starbucks Wi-Fi, so let’s see how my VPS handles a speed test. I’m also concerned about system usage as my VPS is the cheapest one out there.
Running htop alongside the speed test.
Let’s get a baseline of how fast this public Wifi is.
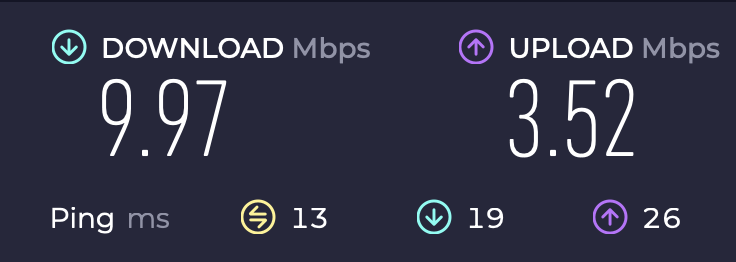
Not too great…
Not what I expected! An improvement, somehow. htop also proved fruitful, with no significant CPU or memory load.
Well, that was a fun afternoon project. Figured I’d learn the process for setting up a VPN and dive deep into answering any questions I didn’t know about.
Wireguard is super easy to set up, especially with a Docker container!
So, running the VPN has been relatively smooth except for a couple of hiccups. Mainly, I learned that VPS droplets are NOT well liked by Financial Services applications and WAFs around the world. Since I’m going through a Digital Ocean droplet, they are flagged for potential spam. Sometimes it’s an extra CAPTCHA, but sometimes access is just denied.
Easy enough to fix – just toggle the VPN off for that transaction and continue as normal. Those types of interactions are encrypted via HTTPS by default, so I’m not too worried about people knowing where I’m visiting.